You are embarking on a vital mission: to construct an earned secure network. This isn’t just about slapping on a few firewalls and calling it a day; it’s about forging a robust digital fortress, one where trust is not a given, but a privilege meticulously earned and continuously validated. In today’s interconnected world, where every click, every data packet, is a potential entry point for adversaries, a perimeter-based security model alone is like building a castle with a moat but leaving the drawbridge perpetually down. You need to adopt a Zero Trust approach, treating every user, device, and application as if it already resides within the trusted network boundaries, and requiring verification before granting access. This meticulous verification process is the cornerstone of an earned secure network.
The concept of Zero Trust is not a single technology, but a security framework that dictates how you design and implement your network. It’s a paradigm shift from implicitly trusting entities within your network to explicitly verifying every request. Think of it like a highly secure building: even if you have a keycard to enter the building, you still need to present it at every doorway, every elevator, and potentially even show identification for access to specific floors or sensitive areas.
The Core Principles of Zero Trust
At its heart, Zero Trust is built on a few fundamental principles that you must internalize. These aren’t merely suggestions; they are the bedrock upon which your entire security infrastructure will stand.
Never Trust, Always Verify
This is the golden rule. No user, device, or network segment is inherently trustworthy. Every access request must be authenticated and authorized. This means moving beyond simple username and password combinations. You need to consider multi-factor authentication (MFA) as a non-negotiable baseline. This adds layers of defense, making it significantly harder for attackers to gain unauthorized access even if they compromise a single credential. Imagine a bank vault: a single key is never enough; you need a combination, a keycard, and perhaps even biometric scans. For your network, think of multiple keys that must be presented simultaneously.
Assume Breach
You must operate under the assumption that your network has already been compromised, or that compromise is inevitable. This perspective forces you to implement granular controls and visibility measures that allow you to detect, contain, and remediate threats quickly. It’s like preparing for a natural disaster: you don’t wait for the hurricane to hit to build your storm shutters. You have them in place, ready to deploy and minimize damage. This principle leads to micro-segmentation, where your network is divided into small, isolated zones, limiting the blast radius of any potential breach. If one segment is compromised, the damage is contained, preventing the attackers from freely moving across your entire infrastructure.
Principle of Least Privilege
Grant users and entities only the minimum permissions necessary to perform their designated tasks. This principle significantly reduces the potential attack surface. If a user only needs read access to a particular database, they shouldn’t have write or delete privileges. This is like ensuring a janitor has access to the office keys, but not the CEO’s private safe. Over-privileging is a common vulnerability that you must actively address by regularly reviewing and revoking unnecessary permissions.
Continuous Monitoring and Validation
Security is not a set-it-and-forget-it endeavor. You must continuously monitor all traffic, user behavior, and device posture. Any deviation from normal patterns should trigger alerts and potentially automated responses. This is akin to having a vigilant security guard who doesn’t just check IDs at the entrance but patrols the halls, observes activity, and reacts to suspicious behavior. Your security tools should provide real-time visibility into network activity, allowing you to spot anomalies before they escalate into full-blown breaches.
Implementing Zero Trust: Key Components
Building a Zero Trust environment requires a multi-faceted approach, integrating various technologies and processes to create a comprehensive security posture.
Identity and Access Management (IAM)
Robust IAM is the cornerstone of Zero Trust. You need to establish a centralized system for managing user identities and their access rights across all your resources. This includes:
- Strong Authentication: As mentioned, implement MFA for all users. Explore advanced authentication methods like biometrics or hardware security keys for highly sensitive access.
- Role-Based Access Control (RBAC): Define roles with specific permissions and assign users to these roles. This simplifies management and ensures consistency.
- Privileged Access Management (PAM): Implement solutions to manage and secure accounts with elevated privileges. These are the accounts that can cause the most damage if compromised, so they require extra scrutiny and control. This involves features like session recording, just-in-time access, and credential vaulting.
- Identity Governance and Administration (IGA): Automate the processes of user provisioning, de-provisioning, and access reviews. This helps maintain the principle of least privilege and reduce the risk of orphaned accounts with excessive permissions.
Endpoint Security
Your endpoints – laptops, desktops, mobile devices, and servers – are critical ingress and egress points for threats. You need to ensure their security is actively managed.
- Endpoint Detection and Response (EDR): Deploy EDR solutions that provide advanced threat detection, investigation, and response capabilities on your endpoints. These tools go beyond traditional antivirus to identify sophisticated threats that might evade simpler detection methods.
- Device Posture Assessment: Before granting access, verify that devices meet security requirements, such as having up-to-date patches, running approved software, and having endpoint security solutions enabled. A compromised device is like a weak link in a chain; it can compromise the entire sequence.
- Mobile Device Management (MDM): For mobile devices, implement MDM solutions to enforce security policies, manage applications, and remotely wipe data if a device is lost or stolen.
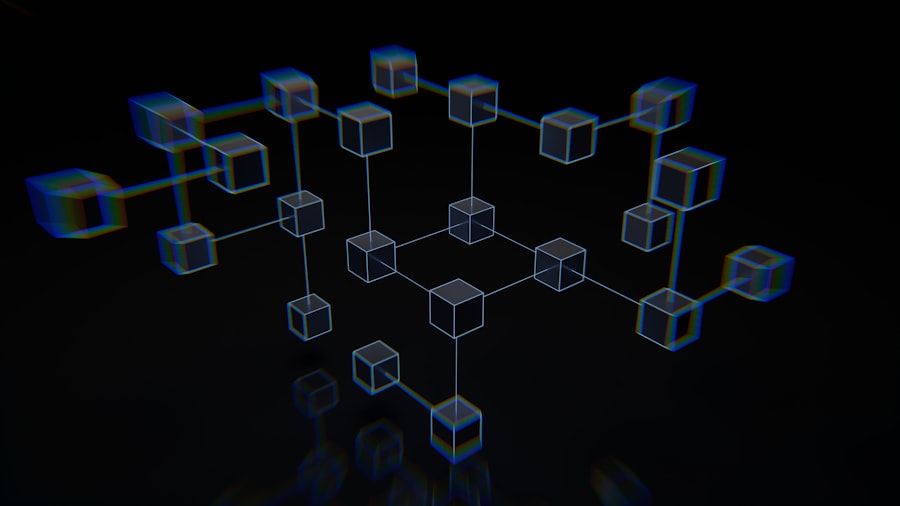
Network Segmentation
Breaking down your large, monolithic network into smaller, isolated segments is crucial for containing breaches.
- Micro-segmentation: This involves creating granular security perimeters around individual workloads or applications, rather than just around network zones. This drastically limits lateral movement for attackers. Imagine dividing your office into individual rooms, each with its own locked door, instead of just having a receptionist at the main entrance.
- Software-Defined Networking (SDN): SDN can greatly simplify the implementation and management of micro-segmentation by allowing you to define and enforce network policies programmatically.
Data Security
Your data is the crown jewel. Protecting it from unauthorized access, modification, or exfiltration is paramount.
- Data Encryption: Encrypt data both at rest (in storage) and in transit (as it moves across the network). This acts as a lock on your data, making it unreadable even if intercepted.
- Data Loss Prevention (DLP): Implement DLP solutions to identify and prevent sensitive data from leaving your network through unauthorized channels. Think of DLP as a diligent librarian carefully checking every book that leaves the library to ensure it’s properly checked out.
- Access Controls for Data: Apply granular access controls to your data stores, ensuring that only authorized individuals or applications can access specific datasets.
Building an earned secure network is crucial for fostering trust and collaboration in both personal and professional relationships. For further insights on this topic, you may find the article on the importance of establishing secure connections particularly enlightening. It discusses various strategies and best practices for creating a supportive environment that encourages open communication and mutual respect. To read more, visit this article.
Building a Culture of Security Awareness
Technology alone is insufficient. An earned secure network requires a complementary shift in human behavior and organizational culture. Your employees are your first line of defense, but they can also be your weakest link if not properly informed and empowered.
Educating Your Workforce
Regular and comprehensive security awareness training is not an optional add-on; it’s an essential investment.
Phishing and Social Engineering Simulations
Conduct regular phishing simulations to test your employees’ ability to recognize and report malicious emails. The results of these simulations should inform further training and reinforce best practices. When an employee can spot a wolf in sheep’s clothing, they prevent chaos from entering the flock.
Best Practices for Password Management
Reinforce the importance of strong, unique passwords and the dangers of password reuse. Encourage the use of password managers. Educate them on the risks of sharing credentials, even with colleagues.
Recognizing and Reporting Threats
Train your employees on how to identify suspicious activity, from unusual emails and pop-ups to unexpected system behavior. Provide clear channels for them to report these incidents without fear of reprisal. Make reporting a part of the regular workflow, like filing a daily report.
Fostering a Security-Conscious Environment
Security should be a shared responsibility, not solely the domain of the IT department.
Leadership Buy-In and Support
Strong support from leadership is critical. When executives champion security initiatives, it sends a clear message throughout the organization about its importance. Visible commitment from the top fosters a cascading effect of security consciousness.
Integrating Security into Processes
Embed security considerations into all business processes and development cycles. Security should not be an afterthought; it should be a fundamental requirement from the inception of any project or workflow. This is akin to ensuring that building codes are considered at the design phase of a skyscraper, not after the foundation is laid.
Feedback and Continuous Improvement
Create mechanisms for employees to provide feedback on security policies and procedures. Regularly review and update your training materials and security protocols based on feedback and evolving threat landscapes. You are in a continuous feedback loop, constantly refining your approach.
Implementing Robust Network Monitoring and Visibility
The ability to see what’s happening on your network in real-time is paramount to building an earned secure network. Without clear visibility, you are effectively flying blind, making it impossible to detect threats or understand the impact of your security measures.
The Importance of Comprehensive Logging
Think of logs as the flight recorder of your network. They capture crucial information that can be used to reconstruct events, identify the source of an attack, and understand how a breach occurred.
Centralized Logging Solutions
Consolidate logs from all your network devices, servers, applications, and endpoints into a central Security Information and Event Management (SIEM) system. This provides a unified view of your security posture and enables correlation of events across different systems. Without centralization, you’re trying to piece together a puzzle with scattered pieces across different rooms.
Log Retention Policies
Establish clear policies for log retention, ensuring that you keep logs for a sufficient period to meet compliance requirements and for forensic analysis. However, balance this with storage costs and privacy considerations.
Log Analysis and Alerting
Configure your SIEM to analyze logs for suspicious patterns and anomalies. Set up alerts for critical security events, enabling your security team to respond rapidly. This isn’t just about collecting data; it’s about extracting actionable intelligence from that data.
Real-Time Network Traffic Analysis
Beyond logs, you need to actively monitor the flow of data across your network.
Intrusion Detection and Prevention Systems (IDPS)
Deploy IDPS to monitor network traffic for malicious activity and to block or alert on potential threats. These systems act as the vigilant sentinels of your network, flagging anything that looks out of the ordinary.
Network Traffic Analysis (NTA) Tools
Utilize NTA tools to gain deeper insights into network behavior, identify unusual communication patterns, and detect advanced threats that might evade traditional signature-based detection. NTA can uncover subtle anomalies that might indicate a stealthy attacker.
Network Access Control (NAC) Solutions
Implement NAC solutions to enforce security policies on devices attempting to access your network. NAC can verify device compliance before granting access, preventing unauthorized or compromised devices from connecting. This is like a bouncer at a club checking IDs and ensuring guests are not bringing in prohibited items.
Implementing Advanced Threat Detection and Response Capabilities

Even with the best preventative measures, threats can still penetrate your defenses. Therefore, you must be prepared to detect, analyze, and respond to these threats swiftly and effectively.
Proactive Threat Hunting
Threat hunting is the proactive search for threats that have evaded your automated defenses. It’s about assuming that you have an intruder and actively seeking them out before they can cause significant damage.
Developing Hunting Playbooks
Create structured playbooks for common threat scenarios, outlining the steps your team should take to investigate and hunt for specific types of malware or attack techniques. These playbooks provide a roadmap for your hunters.
Leveraging Threat Intelligence
Integrate threat intelligence feeds into your detection and hunting processes. This helps you stay informed about the latest threats, attacker tactics, techniques, and procedures (TTPs), and enables you to tailor your hunts accordingly.
Utilizing Advanced Analytics
Employ user and entity behavior analytics (UEBA) and machine learning to identify anomalous behavior that might indicate a compromise. These tools can detect subtle deviations from normal patterns that might escape human observation.
Incident Response Planning and Execution
A well-defined incident response plan is your emergency blueprint for dealing with security breaches.
Incident Response Team (IRT)
Form a dedicated IRT with clearly defined roles and responsibilities. Ensure that team members have access to the necessary tools and authority to act decisively during an incident.
Incident Response Playbooks
Develop detailed playbooks for various types of security incidents, outlining the steps for containment, eradication, recovery, and post-incident analysis. These playbooks are your lifelines during a crisis.
Regular Testing and Drills
Conduct regular incident response drills and tabletop exercises to test the effectiveness of your plan and to ensure that your IRT is prepared to handle real-world scenarios. Practice makes perfect when stakes are this high.
Building an earned secure network is essential for fostering trust and collaboration in any organization. For those interested in exploring this topic further, a related article provides valuable insights into the strategies and practices that can enhance network security and reliability. You can read more about these strategies in the article on network security, which offers practical tips and real-world examples to help you create a robust framework for your organization.
Continuous Improvement and Adaptation
| Metric | Description | Target Value | Current Value | Notes |
|---|---|---|---|---|
| Authentication Success Rate | Percentage of successful authentications without errors | 99.9% | 99.5% | Higher rates indicate better user access control |
| Multi-Factor Authentication (MFA) Adoption | Percentage of users enrolled in MFA | 95% | 87% | Critical for reducing unauthorized access |
| Network Intrusion Attempts Blocked | Number of intrusion attempts detected and blocked per month | 100% | 98% | Reflects effectiveness of intrusion detection systems |
| Patch Management Compliance | Percentage of systems updated with latest security patches | 100% | 92% | Ensures vulnerabilities are minimized |
| Encrypted Traffic Percentage | Percentage of network traffic that is encrypted | 100% | 85% | Encryption protects data in transit |
| Incident Response Time | Average time to respond to security incidents (hours) | <1 hour | 1.5 hours | Faster response reduces damage |
| User Access Reviews | Frequency of reviewing user access rights | Monthly | Quarterly | Regular reviews prevent privilege creep |
The threat landscape is constantly evolving, and so too must your security strategies. Building an earned secure network is not a destination, but an ongoing journey of continuous improvement.
Staying Ahead of Emerging Threats
- Regular Risk Assessments: Conduct periodic risk assessments to identify new vulnerabilities and potential threats to your organization. This is like regularly inspecting the structural integrity of your castle and identifying any weak points that need reinforcement.
- Adopting New Security Technologies: Stay informed about emerging security technologies and evaluate their applicability to your environment. Be willing to invest in solutions that enhance your security posture.
- Industry Best Practices: Follow industry best practices and frameworks, such as NIST Cybersecurity Framework or ISO 27001, to guide your security initiatives.
Measuring Security Effectiveness
- Key Performance Indicators (KPIs): Define and track relevant security KPIs to measure the effectiveness of your security controls and processes. This could include metrics like mean time to detect (MTTD) and mean time to respond (MTTR).
- Regular Audits and Penetration Testing: Conduct regular internal and external audits, as well as penetration testing, to identify weaknesses and validate the effectiveness of your security measures. These are like having independent inspectors rigorously test your defenses.
- Lessons Learned: After any security incident, conduct a thorough post-mortem analysis to identify lessons learned and incorporate them into your security strategy. This ensures that you don’t repeat the same mistakes.
By diligently implementing these strategies, you are not just building a network; you are forging a resilient and trustworthy digital environment, one where security is earned through continuous vigilance, adaptation, and a deep-seated commitment to protecting your valuable assets. You are constructing a fortress not of stone, but of code and policy, where trust is the most guarded commodity.
FAQs
What is an earned secure network?
An earned secure network is a cybersecurity framework where organizations build trust and security through continuous verification, compliance, and proactive risk management rather than relying solely on perimeter defenses.
How does building an earned secure network improve cybersecurity?
It enhances cybersecurity by ensuring that all users, devices, and systems are continuously authenticated and authorized, reducing the risk of breaches caused by insider threats or compromised credentials.
What are the key components of an earned secure network?
Key components include continuous monitoring, identity and access management, zero trust principles, real-time threat detection, and automated response mechanisms.
Who should implement an earned secure network?
Organizations of all sizes, especially those handling sensitive data or operating in regulated industries, should consider implementing an earned secure network to strengthen their security posture.
What challenges might organizations face when building an earned secure network?
Challenges include integrating diverse systems, managing user privacy concerns, ensuring scalability, maintaining up-to-date security policies, and requiring ongoing investment in technology and training.