The battlefield is no longer solely defined by trenches and steel. You stand at the precipice of a new era, where the clash of arms is increasingly drowned out by the hum of servers and the whisper of algorithms. This is the rise of digital warfare, a profound and irreversible shift away from the traditional reliance on human intelligence (HUMINT) as the primary bedrock of strategic advantage. Gone are the days when a well-placed operative behind enemy lines could single-handedly tip the scales of a conflict. Today, the most potent intelligence flows not from hushed confessions in smoky rooms, but from the vast, shimmering ocean of digital data.
HUMINT, for centuries, was the undisputed king of intelligence gathering. It was the art of understanding the human psychology of your adversary, of peeling back the layers of deception with skilled interrogation and covert observation. You might have trained yourself to read the subtle flicker of an eye, the nervous tremor of a hand, or the carefully constructed narrative designed to mislead. This was a war fought in the shadows, relying on courage, intuition, and the deeply ingrained understanding of human motivations.
The Inherent Vulnerabilities of HUMINT
However, this deeply human approach, while often effective, carried inherent vulnerabilities. Each operative represented a single point of failure, a human being susceptible to capture, coercion, or ideological compromise. The sheer volume and velocity of information required in modern conflicts quickly outpaced the capacity of human networks to collect, process, and disseminate it in a timely manner. Imagine trying to map a sprawling metropolis with a single scout on foot, while your adversary is deploying an entire aerial survey fleet.
The Rise of “Dead Drops” and Digital Ghosts
The traditional “dead drop” – a clandestine exchange of information – now has a digital counterpart. Instead of exchanging a coded message in a hidden location, sensitive data can be exfiltrated through compromised networks or social engineering attacks, leaving behind only faint digital footprints. The human element remains, but it is no longer the primary actor; it is often a pawn in a larger digital game, manipulated or unknowingly exploited. Your enemy might not need to capture your operatives; they can simply observe their digital communications, their online activity, and even their biometric data passively collected from ubiquitous devices.
The shift from human intelligence to digital warfare has become a critical topic in today’s rapidly evolving technological landscape. As nations increasingly rely on cyber capabilities for strategic advantages, understanding the implications of this transition is essential. A related article that delves into the complexities of this shift can be found at Unplugged Psychology, where it explores the psychological and societal impacts of digital warfare on modern conflicts.
The Data Deluge: A New Intelligence Landscape
The digital realm has unleashed an unprecedented deluge of data, a veritable tsunami that dwarfs anything previously imaginable. Every online interaction, every transaction, every sensor reading generates a data point, and these points, when pieced together, paint a remarkably comprehensive picture. You are now navigating a world where the sheer volume of available information is overwhelming, and the challenge is not its scarcity, but its management and interpretation.
The Power of Open-Source Intelligence (OSINT)
The decentralization of information has given birth to the powerful discipline of Open-Source Intelligence (OSINT). What was once hidden behind state secrets is now openly available on the internet, from social media posts to satellite imagery, from publicly available financial records to technical specifications of military equipment. You, the reader, can, with the right tools and training, access a vast repository of information that was once the exclusive domain of intelligence agencies. This democratization of information is a double-edged sword, empowering both those who seek truth and those who seek to deceive.
The Quantifiable Metrics of Digital Activity
Beyond passive observation, digital warfare leverages the quantifiable metrics of online activity. The volume of internet traffic in a specific region, the types of websites visited, the keywords used in searches – all these can reveal patterns and intentions. Imagine a doctor monitoring a patient’s vital signs; these digital metrics are the vital signs of a nation, revealing its health, its stress points, and its underlying diseases. For you, this means understanding that every click you make, every search you perform, is a potential data point contributing to a larger intelligence mosaic.
Social Media as a Battlefield of Perceptions
Social media platforms, once mere tools for personal connection, have become potent battlegrounds for shaping perceptions and disseminating narratives. Your ability to discern truth from fiction, to identify coordinated disinformation campaigns, and to understand how public opinion is being manipulated is a critical aspect of modern digital warfare. You are not just a consumer of information; you are a potential target of psychological operations, and your online engagement can be weaponized against you.
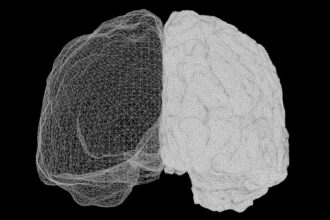
The Automated Analyst: Algorithms as Your New Spies
The sheer scale of digital data necessitates an automated approach to its analysis. Human analysts, no matter how skilled, cannot possibly sift through terabytes of information in real-time. This is where artificial intelligence (AI) and machine learning (ML) step into the breach, becoming your tireless, incorruptible digital spies. They are the silent observers who never sleep, working to identify patterns, anomalies, and threats that would elude the human eye.
Machine Learning for Pattern Recognition
Machine learning algorithms excel at identifying complex patterns in vast datasets. They can detect subtle shifts in communication trends, identify previously unknown connections between individuals or organizations, and flag suspicious activities before they escalate. Think of it as having a legion of highly trained detectives, each capable of analyzing millions of pieces of evidence simultaneously, searching for that one crucial clue. For you, this means realizing that your online behavior is being constantly analyzed by these sophisticated systems, searching for deviations from the norm.
Natural Language Processing (NLP) for Understanding Text
Natural language processing (NLP) allows machines to understand and interpret human language. This is crucial for sifting through the mountains of text data generated online – emails, forum posts, news articles, and encrypted communications. NLP can identify sentiment, extract key entities, and even translate languages in real-time, removing previous barriers to intelligence gathering. Your thoughts, expressed through text, are now fodder for computational interpretation, allowing adversaries to gauge your mood, your allegiances, and your potential responses to various stimuli.
Predictive Analytics: Forecasting the Unseen
The ultimate goal of AI in digital warfare is predictive analytics – the ability to forecast future events and adversary actions. By analyzing historical data and current trends, algorithms can identify emerging threats, anticipate escalations, and even predict the success or failure of specific military operations. This is akin to having a glimpse into the future, allowing you to prepare for what is to come rather than merely reacting to it. You are operating in an environment where your own predictable behaviors can be used to forecast your future actions, potentially before you even make them yourself.
The Cyber Offensive: Weaponizing the Digital Realm

The shift from HUMINT also signifies a parallel shift in offensive capabilities. While HUMINT was primarily about information gathering, digital warfare offers direct offensive capabilities that can cripple an adversary without firing a single shot. The digital realm is no longer just a source of information; it is a weapon itself.
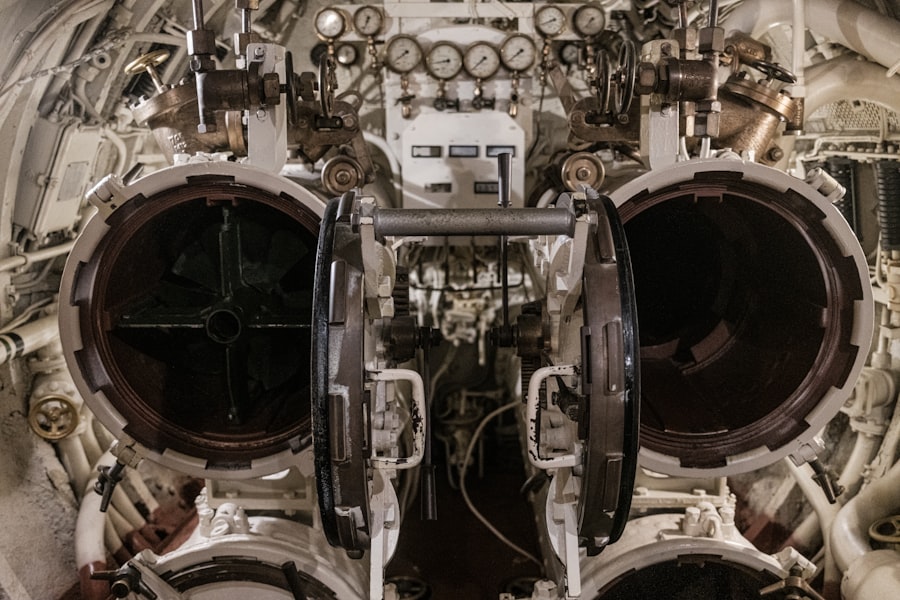
The Anatomy of a Cyberattack
A cyberattack can range from the subtle act of espionage – planting malware to steal sensitive data – to the devastating act of disrupting critical infrastructure. Imagine a phantom limb that can disable an opponent’s entire nervous system without leaving a visible wound. This can involve denial-of-service attacks that flood networks with traffic, ransomware that locks down vital systems, or sophisticated exploits that allow adversaries to gain complete control of targeted systems. You are increasingly vulnerable to these attacks, as more aspects of your life are intertwined with digital infrastructure.
Disrupting Command and Control
One of the most potent offensive applications of digital warfare is the disruption of an adversary’s command and control (C2) systems. By severing communication lines, injecting falsified orders, or disabling critical decision-making platforms, you can effectively paralyze an enemy’s ability to fight. This is like cutting the strings of a puppet master, leaving the puppets floundering and disorganized. Your government’s ability to effectively manage a crisis can hinge on the robustness of its digital C2 infrastructure.
Espionage Through Digital Means
The age-old practice of espionage has been revolutionized. Instead of risking agents to infiltrate secure facilities, adversaries can now utilize sophisticated malware and phishing techniques to gain access to classified information remotely. Imagine a digital spy who can slip through firewalls and antivirus programs with the grace of a ghost, gathering intelligence without ever being physically present. Your personal cybersecurity practices, therefore, become a small but significant bulwark against this pervasive threat.
The evolution of modern conflict has increasingly highlighted the shift from traditional human intelligence to the complexities of digital warfare, where cyber capabilities play a crucial role in national security. This transformation is explored in detail in a related article that discusses the implications of such a shift on global power dynamics. For those interested in understanding the nuances of this topic, you can read more about it in the insightful piece found here. As nations adapt to these new forms of engagement, the importance of digital strategies becomes ever more apparent.
The Diminishing Role of the Human Element (and its Critical Reimagining)
| Metric | Human Intelligence (Traditional) | Digital Warfare (Modern) | Impact/Notes |
|---|---|---|---|
| Information Gathering Speed | Days to weeks | Seconds to minutes | Real-time data collection accelerates decision-making |
| Data Volume Processed | Limited by human capacity | Petabytes and beyond | Big data analytics enable comprehensive intelligence |
| Analysis Accuracy | Subject to human error and bias | Enhanced by AI and machine learning | Improved predictive capabilities and reduced errors |
| Operational Reach | Geographically limited | Global and cyber domain | Expanded battlefield beyond physical borders |
| Response Time | Hours to days | Milliseconds to seconds | Faster threat neutralization and countermeasures |
| Human Risk Exposure | High (field agents, operatives) | Low to moderate (cyber operators) | Reduced physical risk but increased cyber vulnerabilities |
| Cost Efficiency | High operational costs | Lower marginal costs after infrastructure | Digital tools reduce manpower and logistics expenses |
| Vulnerability | Physical capture or compromise | Cyber attacks, hacking, misinformation | New types of threats require advanced cybersecurity |
While the article title suggests a shift from human intelligence, it’s crucial to understand that the human element is not entirely obsolete. Instead, its role is being fundamentally reimagined and, in some ways, elevated. The strategist who can interpret the algorithmic output, the ethical officer who can guide the development of AI, and the diplomat who can navigate the complex geopolitical landscape of cyber conflict all remain indispensable.
The Importance of Human Oversight and Intent
Even the most sophisticated AI systems operate based on the parameters and objectives set by humans. The ethical implications of using AI in warfare, the potential for unintended consequences, and the need to ensure that technology serves human goals rather than dictates them are all critical areas where human intelligence remains paramount. You must be aware that the algorithms making decisions in the digital battlefield are guided by human intent, and that intent can be flawed or malevolent.
The Art of Strategic Interpretation
The raw data analyzed by AI needs to be interpreted within a broader strategic context. Human analysts are still required to understand the geopolitical landscape, the cultural nuances of an adversary, and the long-term implications of digital actions. The algorithm might identify a threat, but it is the human strategist who decides how to respond, weighing the risks and rewards of various courses of action. You are not just a passive observer of this shift; you are part of the human element that must understand and adapt to it.
The Future of HUMINT in the Digital Age
The future of HUMINT lies in its integration with digital intelligence. Operatives can now be equipped with advanced digital tools to gather information discreetly, analyze data on the fly, and communicate securely. The human element can act as a crucial “ground truth” validator for AI-generated intelligence, providing context and nuance that machines may miss. Imagine a digital Sherlock Holmes, using advanced forensic tools and AI assistance to solve crimes that were once impossible to crack. Your role, as an informed individual, is to understand how your own digital footprint is becoming a component of this evolving intelligence ecosystem. The rise of digital warfare does not signal the end of human intelligence, but rather its transformation into a more integrated, data-informed, and strategically crucial component of national security. You are living through this radical metamorphosis, and your understanding of it is now more vital than ever.

▶️ WARNING: Your Phone Is Interrogating You
FAQs
What is meant by the shift from human intelligence to digital warfare?
The shift from human intelligence to digital warfare refers to the transition in military and security operations from relying primarily on human agents and traditional espionage methods to utilizing advanced digital technologies, cyber tools, and automated systems to gather intelligence, conduct operations, and engage in conflict.
How has digital warfare changed intelligence gathering?
Digital warfare has transformed intelligence gathering by enabling the collection and analysis of vast amounts of data through cyber surveillance, hacking, satellite imagery, and artificial intelligence. This reduces the dependence on human spies and allows for faster, more precise, and often remote intelligence operations.
What are some common tools used in digital warfare?
Common tools in digital warfare include malware, ransomware, phishing attacks, cyber espionage software, artificial intelligence algorithms, drones, and electronic warfare systems. These tools are used to disrupt, deceive, or gather information from adversaries in cyberspace.
What are the risks associated with the shift to digital warfare?
Risks include increased vulnerability to cyberattacks, potential loss of privacy, escalation of conflicts through cyber means, difficulty in attribution of attacks, and the possibility of unintended consequences such as collateral damage to civilian infrastructure.
How does digital warfare impact traditional military strategies?
Digital warfare requires traditional military strategies to adapt by integrating cyber defense and offense capabilities, emphasizing information security, and developing new doctrines that address the speed and complexity of cyber operations alongside conventional warfare tactics.