You are an intelligence operative, tasked with navigating a labyrinth of information and clandestine operations. In this digital age, the very act of seeking or disseminating information can be a high-stakes gamble, a tightrope walk over a chasm of surveillance. To succeed, you need tools that offer not just anonymity, but a robust shield against prying eyes. This is where Tor, the Onion Router, enters the operational lexicon. It’s not a magic wand, but a meticulously engineered system, a digital cloaking device that allows you to conduct your work with a significantly reduced risk of exposure. Understanding Tor, its strengths, and its limitations, is paramount to your effectiveness in the shadows.
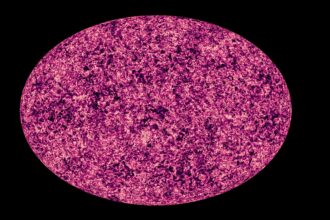
Tor is not a single program; it’s a network and a protocol. Think of it as a vast, decentralized digital relay race, where your data packets are passed from one volunteer-run server, or “node,” to another, before reaching their final destination. Each node only knows about the packet it received and the packet it sends next. This layered approach is what gives Tor its name: the “onion” metaphor, where each layer of encryption is peeled back by a successive node until the plaintext data is revealed at the exit node.
How Data Travels Through Tor
Your communication originates from your device and is wrapped in multiple layers of encryption, akin to placing a letter in progressively more secure envelopes. The first key encrypts the data for the first node, the second key for the second node, and so on, until the final layer is encrypted for the exit node.
The Entry Node: Your First Shield
When you initiate a Tor connection, your traffic is first directed to an “entry node.” This node is unaware of your original IP address; it only knows that it received your encrypted data from the Tor network. Its role is to decrypt the outermost layer of encryption and forward your packet to the next node in the circuit.
The Middle Nodes: The Relay Express
Your data then travels through a series of “middle nodes.” These nodes perform a similar function: decrypting one layer of encryption and passing the data along. Crucially, each middle node only knows the IP address of the node it received the data from and the IP address of the node it’s sending the data to next. This prevents any single node from having a complete picture of your communication path.
The Exit Node: The Bridge to the Destination
Finally, your data reaches the “exit node.” This is the node that actually connects to the destination website or service you are trying to access. The exit node decrypts the final layer of encryption, revealing your original data in plaintext. It then sends this data to the destination, but the destination website sees the IP address of the exit node, not yours. This is where the illusion of anonymity is largely maintained in relation to the destination.
Encryption: The Bedrock of Security
Tor’s security hinges on robust encryption. You’re not just sending data; you’re sending data that has been meticulously sealed multiple times.
Symmetric Encryption at Each Relay
At each relay point (entry, middle, and exit nodes), a form of symmetric encryption is employed. This means the same key is used for both encrypting and decrypting the data at that specific stage. However, each node possesses only the specific key needed to decrypt its layer.
Asymmetric Encryption for Key Exchange
When establishing a connection, asymmetric encryption plays a vital role. This is a system where two keys are used: a public key for encryption and a private key for decryption. This allows for secure key exchange between nodes, ensuring that the correct encryption keys are used throughout the circuit.
For those interested in enhancing their secure communication practices, a related article that provides valuable insights on using Tor for intelligence purposes can be found at this link. This resource outlines the essential steps and considerations for leveraging Tor’s anonymity features, ensuring that sensitive information remains protected from prying eyes.
Navigating the Network: Tor Browser and Beyond
While the Tor network is the underlying infrastructure, you will most likely interact with it through the Tor Browser. Think of the Tor Browser as your specialized vehicle for navigating the Tor network. It’s pre-configured and optimized to route all your web traffic through the Tor network.
The Tor Browser: Your Integrated Solution
The Tor Browser is a modified version of Firefox, designed with privacy as its core principle. It bundles everything you need to use Tor, making it relatively simple to get started.
Pre-configured for Privacy
Unlike standard browsers, the Tor Browser is pre-configured to block trackers, prevent browser fingerprinting, and ensure that all your connections are routed through the Tor network by default. This eliminates the need for complex manual configuration.
JavaScript and Scripts: A Double-Edged Sword
While JavaScript can enhance web interactivity, it can also reveal your identity. The Tor Browser allows you to adjust security levels to disable JavaScript on potentially risky sites, understanding that some websites may not function correctly with JavaScript disabled. This is a crucial setting to manage, balancing functionality with security.
Beyond the Browser: Other Tor Applications
While the Tor Browser is the most common entry point, Tor can also be used to secure other types of traffic.
Secure Shell (SSH) with Tor
For system administrators or those needing to establish secure remote command-line access, configuring SSH to tunnel through Tor is a valuable technique. This allows you to manage remote servers anonymously, shielding your connection from direct observation.
Email and Messaging Over Tor
Certain email clients and messaging applications can be configured to use Tor for their connections. This adds an extra layer of anonymity to your communications, making it more difficult to trace the origin of your messages. However, the security of the content itself still relies on end-to-end encryption within the messaging protocol.
Operational Considerations: Strengths and Weaknesses

Tor is an indispensable tool for intelligence operations, but like any tool, it has its limitations. A thorough understanding of these nuances is crucial for effective deployment.
Strengths for Intelligence Operatives
When used correctly, Tor offers significant advantages for your clandestine activities.
Anonymity and Pseudonymity
Tor’s primary strength lies in its ability to anonymize your internet traffic. It obscures your IP address, making it incredibly difficult for adversaries to determine who you are or where you are connecting from. This is vital for maintaining operant anonymity.
Circumvention of Censorship
In regions where internet access is heavily restricted or monitored, Tor can serve as a vital conduit for accessing uncensored information or communicating with sources outside these oppressive regimes. It’s a digital escape hatch.
Protection Against Network Surveillance
By randomizing your connection path and encrypting your data at multiple layers, Tor makes it significantly harder for network surveillance tools to track your online activities, correlate your traffic with your identity, or conduct traffic analysis.
Weaknesses and Potential Vulnerabilities
No system is impregnable. Recognizing Tor’s potential vulnerabilities allows you to mitigate risks and employ complementary security measures.
Exit Node Vulnerabilities: The Final Gateway
The exit node is the point of least security in the Tor chain, as it decrypts your traffic. If an adversary controls a significant number of exit nodes, they could potentially monitor and analyze the unencrypted traffic passing through them. This is a critical point to consider.
Correlation Attacks: The Long Game
While individual Tor connections are anonymized, sophisticated adversaries might attempt to correlate patterns of your online activity with your real-world movements or other identifying information over an extended period. This is a persistent threat that requires vigilance.
Bandwidth Limitations and Latency
The multi-hop nature of Tor can lead to slower connection speeds and increased latency compared to direct internet connections. For real-time operations requiring high bandwidth, this can be a significant drawback, necessitating careful planning and consideration.
User Error and Operational Security (OpSec)
The most effective security system can be compromised by user error. If you fail to adhere to strict operational security (OpSec) practices, such as accidentally revealing identifying information within Tor, your anonymity can be compromised. Tor is a tool; your habits are the crucial variable.
Mitigating Risks: Enhancing Your Tor Usage

To maximize the effectiveness of Tor in your operations, you must adopt a multi-layered approach to security. Think of it as reinforcing your digital fortress.
Practicing Strict Operational Security (OpSec)
Your actions outside of the Tor network are as important as your actions within it.
Avoid Logging Into Personal Accounts
When using Tor for activities where anonymity is paramount, never log into personal accounts (email, social media, cloud storage) that are linked to your real identity. This is a direct route to self-exposure.
Be Mindful of Metadata and Digital Footprints
Even when using Tor, be conscious of the metadata generated by your activities. This includes timestamps, file properties, and any information that could inadvertently link your online actions to your offline identity.
Isolate Tor Usage
Consider using a dedicated operating system or virtual machine solely for Tor-based activities. This creates a clean and isolated environment, minimizing the risk of cross-contamination with your regular computing activities.
Choosing Reputable Exit Nodes (Limited Control)
While you cannot directly choose your exit node, understanding the risks associated with them is important.
Diversity of Exit Nodes
The Tor network benefits from a large and diverse pool of exit nodes. This makes it harder for any single entity to control a significant portion of them and conduct widespread attacks.
Monitoring for Suspicious Activity
If you observe consistently slow speeds or unusual behavior when connecting to specific websites via Tor, it might warrant further investigation or a change in your approach. However, direct control over exit nodes is not within your purview on the standard network.
Complementary Security Measures
Tor is most effective when integrated with other security protocols and practices.
Virtual Private Networks (VPNs) in Tandem with Tor (VPN over Tor)
While often considered an either/or choice, a “VPN over Tor” configuration can enhance security. Your traffic first goes through the VPN, then into the Tor network. This hides your Tor usage from your VPN provider and can offer an additional layer of protection against some traffic analysis by your Internet Service Provider (ISP).
End-to-End Encryption for Content
Remember that Tor anonymizes the connection, not necessarily the content of your communication. For sensitive messages, always use strong end-to-end encryption protocols (e.g., PGP for email, Signal for messaging) within your Tor-secured applications. This ensures that even if your traffic is intercepted at the exit node, the content remains unreadable.
For those interested in enhancing their secure communication methods, using Tor can be an effective solution. It provides anonymity and protects your data from prying eyes, making it particularly useful for intelligence-related activities. To delve deeper into the intricacies of using Tor for secure communication, you might find this insightful article on the topic helpful. You can read more about it here.
Advanced Tor Techniques: For the Discerning Operative
| Step | Action | Description | Security Consideration | Tools/Resources |
|---|---|---|---|---|
| 1 | Download Tor Browser | Obtain the official Tor Browser from the Tor Project website. | Ensure download is from official source to avoid tampered software. | Tor Project |
| 2 | Install and Configure | Install the browser and configure security settings to ‘Safest’ mode. | Disabling scripts and plugins reduces attack surface. | Tor Browser Security Settings |
| 3 | Use End-to-End Encrypted Communication | Use encrypted messaging services (e.g., Signal, OTR chat) over Tor. | Tor anonymizes traffic but does not encrypt content end-to-end. | Signal, OTR, PGP |
| 4 | Access .onion Services | Use Tor to access hidden services for secure communication. | Onion services provide anonymity for both parties. | Tor Browser, Onion URLs |
| 5 | Maintain Operational Security (OpSec) | Avoid revealing personal information and use separate identities. | Prevent correlation attacks and deanonymization. | Separate devices/accounts, VPN (optional) |
| 6 | Regularly Update Tor | Keep Tor Browser updated to patch vulnerabilities. | Outdated software can be exploited. | Tor Project Updates |
| 7 | Use Bridges if Tor is Blocked | Configure bridges to bypass censorship. | Helps maintain access in restrictive environments. | Tor Bridges |
For those who require an even higher degree of compartmentalization and security, advanced Tor techniques can be employed. These methods demand a deeper understanding of network protocols and system configuration, but offer a more robust defense.
Tails: The Live Operating System
You are looking for a digital ghost, and Tails is that very apparition. Tails (The Amnesic Incognito Live System) is a security-focused, Linux-based operating system that you can boot from a USB stick or DVD. It is designed to leave no trace on the computer it’s used on.
Amensia Functionality
When you shut down Tails, all information is erased from RAM, meaning no traces of your activity remain on the host machine. This is akin to a clean slate every time you disconnect.
Pre-configured Tor Integration
Tails routes all internet traffic through the Tor network by default. This means any application you use within Tails is automatically anonymized without requiring any manual configuration. It’s an out-of-the-box stealth solution.
Onion Services: Darker Corners of the Web
Tails also provides enhanced support for accessing Onion Services, also known as hidden services. These are websites and services that are exclusively accessible through the Tor network, offering a higher degree of anonymity for both the server and the client.
Whonix: The Dual-Part System
Whonix is another security-focused operating system distribution designed for advanced anonymity. It operates as a two-part system: a Gateway machine and a Workstation machine.
Separation of Concerns
The Gateway machine is solely responsible for connecting to the Tor network, effectively acting as a Tor proxy. The Workstation machine then connects to the Gateway, ensuring that all its network traffic is routed through Tor. This separation significantly reduces the attack surface.
Preventing IP Leaks
This dual-system architecture is highly effective at preventing IP address leaks. Even if the Workstation is compromised, it cannot directly expose your real IP address because it has no direct internet connection and can only communicate with the Gateway.
For Detailed Investigations
Whonix is particularly suited for operatives who need to conduct extensive research, download sensitive documents, or interact with web services where a persistent and highly anonymized environment is critical.
Conclusion: Tor as a Cornerstone of Secure Communication
As you delve deeper into the world of intelligence gathering and secure operations, Tor emerges not as a casual browsing tool, but as a potent instrument for maintaining operational integrity. It is a conduit for information, a shield against surveillance, and a facilitator of clandestine communication. However, remember that Tor is not a solitary solution but a vital component of a comprehensive security strategy.
The Ongoing Battle for Digital Privacy
The digital landscape is a constantly evolving battlefield. Adversaries are resourceful, and their methods of surveillance are ever-advancing. Your ability to adapt and leverage tools like Tor effectively will be a defining factor in your success.
Knowledge as Your Strongest Defense
Your understanding of how Tor works, its inherent strengths, and its potential weaknesses is your most crucial defense. Complacency is your enemy. Continuously educate yourself, refine your operational security, and always be aware that the digital realm demands vigilance.
Tor: An Essential Tool in Your Arsenal
When wielded with knowledge, discipline, and a robust understanding of operational security, Tor empowers you to navigate the complex and often perilous digital currents of modern intelligence work. It is a cornerstone, a vital piece of infrastructure in your ongoing mission to operate securely and effectively in the world of information.

▶️ WARNING: Your Phone Is Interrogating You
FAQs
What is Tor and how does it enhance secure communication?
Tor, short for The Onion Router, is a network that enables anonymous communication by directing internet traffic through a series of volunteer-operated servers called nodes. This process encrypts and routes data multiple times, making it difficult to trace the origin or destination, thereby enhancing privacy and security in communication.
How can intelligence professionals use Tor for secure communication?
Intelligence professionals can use Tor to protect their identity and location when exchanging sensitive information. By accessing communication platforms or sending messages through the Tor network, they reduce the risk of interception, surveillance, or tracking by adversaries or unauthorized parties.
Is Tor completely secure for confidential intelligence communication?
While Tor significantly improves anonymity and security, it is not infallible. Users must follow best practices, such as avoiding revealing personal information, using end-to-end encrypted communication tools, and keeping software updated. Combining Tor with other security measures enhances overall protection.
What are the limitations or risks of using Tor for intelligence communication?
Tor can be slower than regular internet connections due to multiple relays, which may affect real-time communication. Additionally, exit nodes can potentially monitor unencrypted traffic, so using encrypted communication protocols is essential. There is also a risk of targeted attacks or de-anonymization if operational security is compromised.
How do I get started with using Tor for secure communication?
To start using Tor, download and install the official Tor Browser from the Tor Project website. For secure communication, use Tor in conjunction with encrypted messaging services or email providers that support end-to-end encryption. Always follow security guidelines and stay informed about updates and best practices.